My OSCP Journey, Review, Timelines And Resources
This blog contains my honest review and oponion on OSCP Exam organized by Offensive Security. I am going to discuss about my OSCP journey, it’s lab and exam review, The whole timeline from begining...
This blog contains my honest review and oponion on OSCP Exam organized by Offensive Security. I am going to discuss about my OSCP journey, it’s lab and exam review, The whole timeline from begining...
We are given the source code for the website hosted , There is a feature that will tell you the time you will get your true love. That time is Evaluate with the help of a eval() function and the ev...

The journey starts with a new VHOST that i got from the DNS of ssl certificate , Gitlab is hosted on the new vhost.The Current version of the gitlab-ce is vulnerable to LFI and RCE exploiting the R...

Altering the administrator username by changing the roleid and login as admin on the web , two ways to get user one is admin page revealing a new VHOST which is running on laravel , and the lavare...

There are two features on webiste ONLINE JSON BEAUTIFIER & VALIDATOR the validator feature is vulnerable to a CVE and after searching about it bit more got initial shell as user , Privlege esca...

There was a reverse tabnabbing in hackthebox in the walkthrough section due to the html link opener using target=”_blank” without any rel=”noopener nofollow” , that results redireting the victim u...
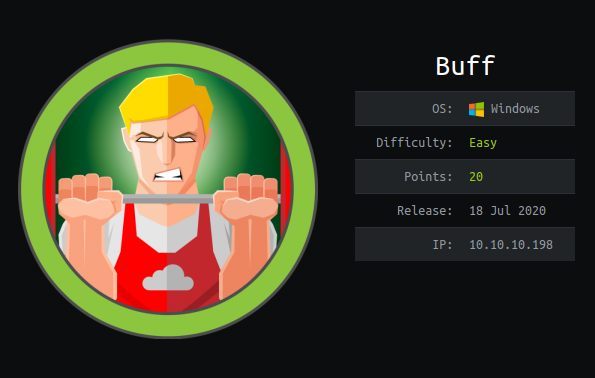
This is relatively an easy box which is based on the 2 CVE’S , The PHP webapp that is hosted on port 8080 is vulnerable to a Unauthenticated Remote Code Execution from that exploit got first initia...

Nmap exposing a new domain , Grabbing employees emails from a webpage . Using swaks to send Spoofed email to all the 57 emails to phish an employee . Got a Username and password , Login into the im...

Discvering a new domain and adding it to the hosts file , Identifying a Local-file-Inclusion and extracting sensitive information . Fuzzing some dirs and got the tomcat-users.xml which contain user...
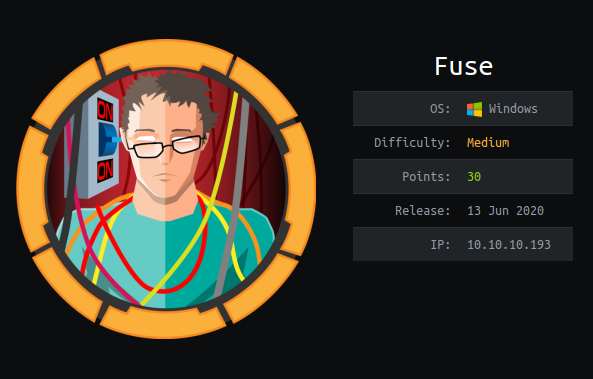
Got few usernames from the files from the website itself and making a custom wordlist from the website itself using cewl . Password Sparying using metasploit on the smb protocol , Got the correct u...